
How Malware Gets Into a WordPress Website
Learn how malware can get into your WordPress website, from pirated plugins and leaked credentials to plugin vulnerabilities and weak server security.
Lately I have been receiving more WordPress cleanup projects with the same general pattern:
That is the main reason I wanted to write this article: cases like this no longer feel rare.
I keep seeing the same pattern repeat. In one hosting account, one website gets hit first, then the other websites in the same environment begin showing similar symptoms. In other cases, the homepage still looks “normal,” but strange files keep reappearing in the file manager. I have also seen the worst-case scenario: the database gets damaged or lost, there is no clean backup, and the website has to be rebuilt from scratch.
That is why I do not want this to read like a generic security article. I want to approach it from a more practical angle:
If your website is already showing signs like strange redirects, gambling pages in Google, Japanese spam indexing, or suspicious files that keep coming back, continue with How Malware Gets Into a WordPress Website, 7 Signs Your WordPress Website Is Infected with Malware and How to Fix It, or go directly to our WordPress malware removal service if you need immediate help.
To make this more concrete, here are two types of cases that genuinely came in recently. I am rewriting them in a more anonymous form, but the patterns are real.
In one case, a single hosting account contained three WordPress websites.
The worst one had already been reset at the WordPress and database level. On the surface it looked clean and newly rebuilt, but every night around midnight it turned back into a gambling website. At the same time, Google indexing had already been polluted, including the search result titles and favicon.
The second website in the same account showed a different symptom: a suspicious folder kept reappearing with the same name even after it was deleted.
The third website still looked relatively alive, but strange files kept being added in the file manager even though the visibly compromised page had already been removed.
To me, a pattern like this clearly shows that the problem is not just one bad file. This is already a hosting environment and persistence problem at a broader level.
Another case was even more concerning from a scope perspective.
It started with a simple “can you check this?” request. But as the conversation continued, it turned out there were roughly 4 or 5 websites with similar issues inside related hosting environments.
That matters because many website owners still think of malware as a one-website, one-time problem. In practice, I often see infections show up in clusters.
If one website is already compromised, there is a real chance another website in the same environment has also been exposed, even if the symptoms are not visible yet.
If I summarize the recent projects that came in, the pattern usually looks something like this:
In some cases, clients place several WordPress websites under the same hosting account.
On the surface, that feels efficient. One account, multiple sites, lower cost.
But once one website is compromised, the risk often does not stop there. Other websites in the same account or environment can become exposed too, especially if isolation is weak or file access is too loose.
That is why malware cases in shared environments often feel strange. The client believes only one website is affected, while in reality more than one website may already be exposed or queued up for exploitation.
This is one of the most frustrating symptoms website owners encounter.
A strange file or folder is deleted today, then tomorrow or the next day it appears again. Sometimes the folder name is the same. Sometimes the files appear in different places. Sometimes the homepage looks clean, but persistence is still active in the background.
For me, this symptom usually means one thing: the real infection source has not been found yet.
Only the symptom was removed, not the root of the problem.
That could mean there is still:
I have also seen a very disturbing pattern like this:
the website is reset, WordPress is reinstalled, the database is cleaned, the homepage looks normal, but at a certain time the website switches back into a gambling site.
Once it reaches that stage, the issue is almost certainly not just “one suspicious file.”
There is some persistence mechanism deliberately placed so the infection can reactivate after a surface-level cleanup. That is why I often remind clients that reinstalling WordPress alone does not automatically solve the problem.
If the entry point and persistence layer are not cut off, the website can look recovered for a moment and then break again.
Many people only panic when the homepage changes or the site starts redirecting.
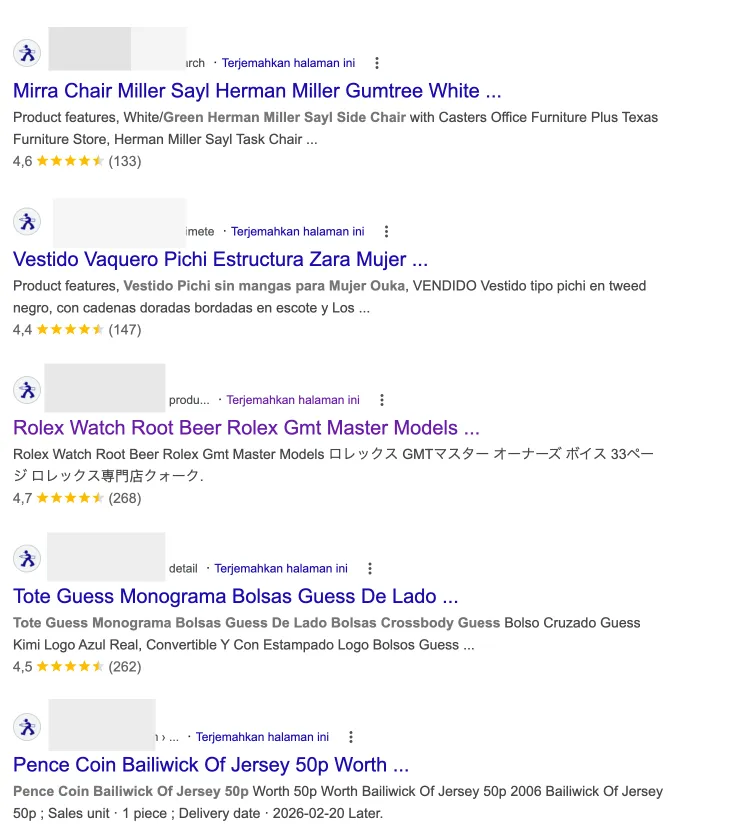
But the heavier damage is often already sitting inside Google search results.
I have seen cases where:
At that point, the problem is no longer only security. SEO is already damaged too.
And once the legitimate index has been replaced by spam, recovery is not always immediate. Even after the files are cleaned, the traces left in Google Search still need to be handled one by one.
In my view, many website owners still think of malware as a technical annoyance.
But in the worst cases, the loss is far more serious than that.
The damage I worry about is not only:
but also:
When a business website disappears, the damage usually comes from both directions at once:
And if that rebuild happens in panic mode, it is often more expensive than the preventive work that could have been done much earlier.
This is one of the most common misconceptions.
As soon as people see a suspicious file in the file manager, they tend to think:
“If I delete this file, the problem is gone.”
Unfortunately, in many cases that is not enough.
Modern WordPress malware rarely depends on one obvious file. It can leave traces in many places:
.htaccess,If one file is deleted but the original entry point is still open, the attacker can come back or a leftover script can restore the same infection.
That is why I am usually very careful with websites that people say were “already cleaned several times,” but the same symptoms keep returning. Usually the issue is not that the hosting is “weird.” The issue is that the previous cleanup never covered the full attack surface.
I understand the urge to fix anything that looks wrong as fast as possible when the site is in chaos. But there are several reactions that often make the situation harder to recover from:
If the original access path is still open or the backdoor is hidden somewhere else, reinstalling WordPress only cleans the visible surface.
If the malicious file really is isolated, this may appear to work for a while. But if the actual problem lives in admin users, the database, scheduled tasks, or another site inside the same hosting account, the infection will return.
This is a common trap. A client feels safe because a backup exists, but that backup was created after the infection had already entered the system.
The result is predictable: the site looks restored, then the symptoms come back.
If you change the WordPress password but do not audit hosting access, FTP, database credentials, and other admin accounts, you have not really closed the door.
Every case is different, but in general my approach usually looks like this:
If several websites sit under the same hosting account, I usually treat them all as suspicious first.
That matters, because cleaning one site while leaving another infected often creates a loop where the same problem keeps returning.
I usually want to know:
Without that, cleanup often becomes random file deletion without direction.
Proper cleanup is rarely just a file manager job.
The areas that often need inspection include:
If spam pages, gambling pages, or Japanese spam pages have already been indexed, the job is not finished even after the website is technically clean.
Google indexing also needs attention.
That is why I consider proper malware cleanup to require two results at once:
After cleanup, I prefer to move directly into prevention:
If those root issues stay in place, the same website can easily return to the same condition a few months later.
I know most clients focus on one thing:
“I just need my website to work normally again.”
That makes sense. But once the site is normal again, the more important question becomes:
how do we stop this from happening again?
At that point, I think three areas matter the most.
If a WordPress website supports a business, maintenance is not an extra task. It is part of the basic defense layer.
And by maintenance, I do not just mean clicking the update button. I mean a more complete routine:
If you want a more structured route, see our website maintenance service and also read Why WordPress Maintenance Matters.
If several websites sit under one hosting account and one of them has already been compromised, I usually recommend a serious review of the foundation.
That does not mean all shared hosting is automatically bad. It is not that simple.
But for a business website, I feel more comfortable when the foundation is more disciplined:
If you want to think more carefully about the hosting side of the problem, continue with When Your Website No Longer Fits Its Current Hosting or Why Business Owners Often Prefer Managed Hosting Over Control Panels.
The most expensive cases I have seen were not just hacked websites. They were websites that could no longer be restored because the backup did not exist or was not usable.
If the database is corrupted, the files are damaged, and there is no clean backup, the remaining option is often a rebuild.
That is why I always see backups as part of business strategy, not a technical checklist.
If I had to answer in one sentence:
because the problem usually comes from a combination of a loose foundation, delayed maintenance, an unhealthy hosting environment, and a security process that has been too reactive for too long.
A website usually does not turn into a gambling site because of one dramatic moment.
It turns because several doors were left open for too long.
And by the time the attack becomes visible on the surface, the damage has often already spread to:
If your website is currently showing signs like:
then I would not stop at “delete the suspicious file.”
Start with a more complete response.
You can:
For me, the real goal is not just “make the website work again today,” but to stop your business website from staying in a permanently vulnerable state.

Founder of Harun Studio, web developer, blogger, and hosting reviewer. He helps business owners build healthier websites through design, development, and long-term maintenance.
Explore more insights that connect closely with this topic.

Learn how malware can get into your WordPress website, from pirated plugins and leaked credentials to plugin vulnerabilities and weak server security.

Learn how to identify a WordPress website infected with malware through 7 hidden signs and find effective ways to fix it quickly.

Explore why WordPress maintenance matters for your website's security, performance, and stability.